Ad Solutions worth Yodeling About
Yahoo Advertising offers omnichannel solutions and powerful data to engage with our brands and deliver results.


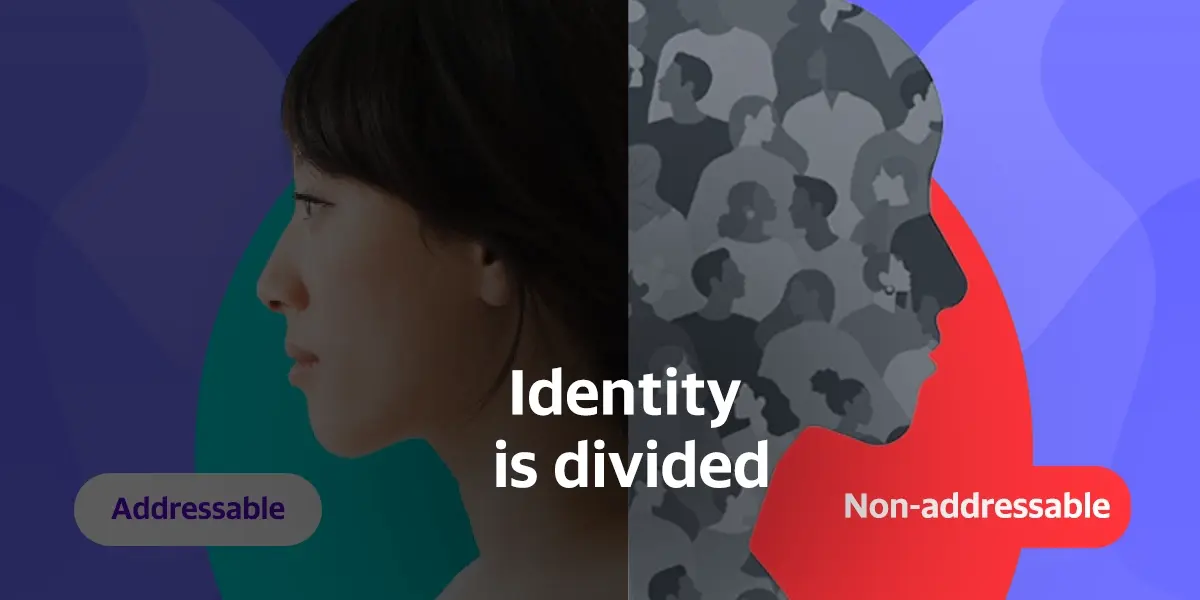
A DSP with the best of both worlds
The transparency of the open internet, with all the scale of a walled garden. We're kind of the whole package, if we do say so ourselves.
Yahoo DSP
Some things to Think About

Don't just take our word for it
Learn how our solutions have helped global brands reach their audiences in unexpected ways.
Get inspiredSuccessful
Oops! Something went wrong while submitting the form.


.webp)